

OPTEAMIZE CLOUD SOLUTIONS PVT LTD had their WordPress farm hosted in a shared hosting space. The entire setup worked perfectly fine for most use cases. However, our client—an expert in Digital Marketing with a proven track record—began noticing a steep spike in traffic to their WordPress sites, far higher than expected even after accounting for results from their digital optimization workflow.
Competing brands were identified as the source of this surge. They constantly polled our client’s website, both manually and through change-tracking bots that captured every modification made to the site. As a result, the traffic included both genuine visitors from the digital marketing efforts and random additional traffic generated by bots.
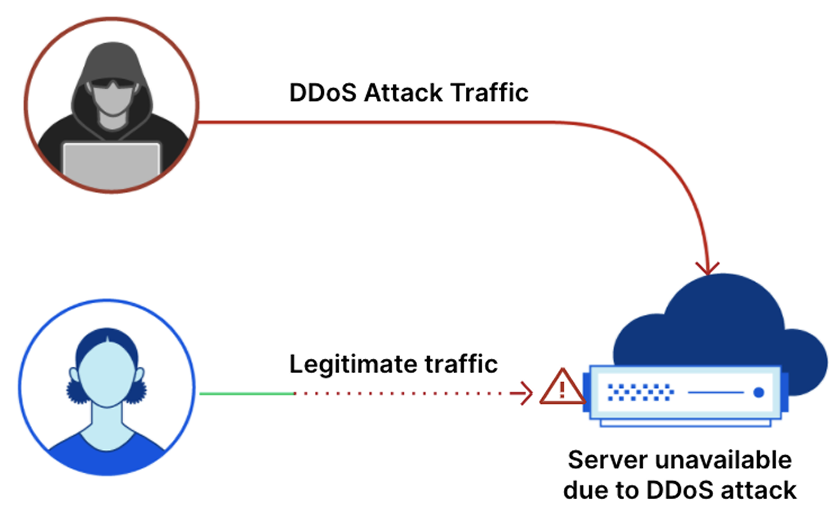
Over time, the density of bot traffic exceeded normal levels, consuming bandwidth meant for real users. On deeper investigation, this activity was classified as a Distributed Denial-of-Service (DDoS) attack. The malicious traffic was designed to overload the server, drain resources, and make the website inaccessible to genuine visitors.
Although the hosting provider had basic safeguards—like blocking some violating IPs—these measures proved insufficient to handle the intensity and persistence of the attack.
At this point, after performing various analyses of the WordPress and server logs, we were able to identify the root cause of the issue, understand the situation, and conclude the need for a better hosting environment with additional capabilities related to roles and permissions. For example, WordPress has plugins like Wordfence which provide security at the application level. However, the traffic still enters the WordPress layer before being filtered, leaving potential exposure.
“Switching to AWS allowed us to stop threats before they reached WordPress, giving us security at the infrastructure level, not just the application.”
To achieve this, we replaced the infrastructure with Amazon Web Services, which provides facilities like WAF (Web Application Firewall) that filter traffic before it reaches the application layer. This proactive approach ensures better security and a more resilient environment for both the application and its users.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
Block quote
Ordered list
Unordered list
Bold text
Emphasis
Superscript
Subscript